 I’ve known about Hackaday for a while, both the professionally curated site hackaday.com and the public participation site hackaday.io. Some of the people behind the site are nearby which allowed me to easily attend some of their local events.
I’ve known about Hackaday for a while, both the professionally curated site hackaday.com and the public participation site hackaday.io. Some of the people behind the site are nearby which allowed me to easily attend some of their local events.
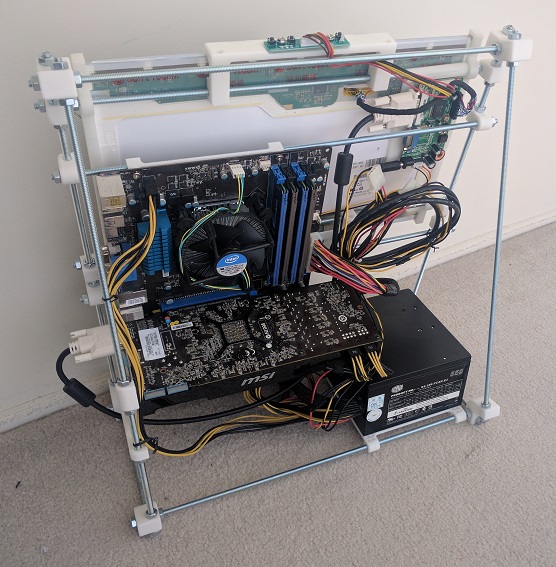
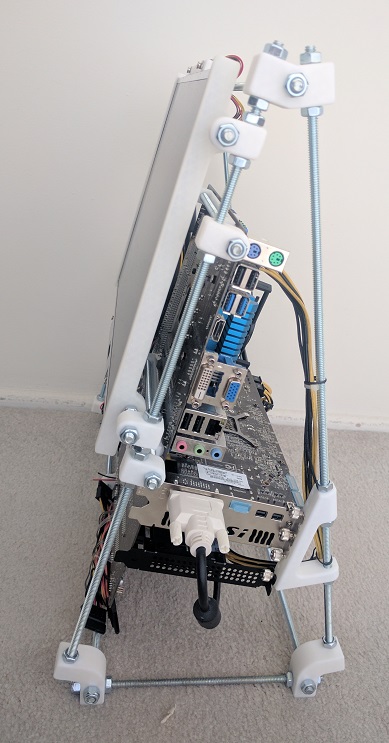
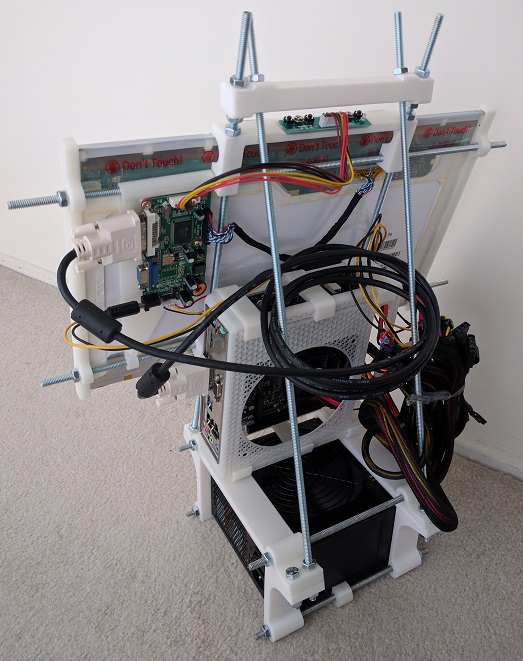
Most of the project pages I browsed through dealt with Arduino boards, Raspberry Pi boards, or even lower-level hardware. I wasn’t sure if a home built PC is the right kind of topic for the site until I brought my current prototype to one of these local meets. The staffers present assured me that it’d be a great project to document on hackaday.io.
All right then! I’ve created a project page to document my work so far, and I’ll continue documenting future iterations over there instead of here.
One of the Hackaday staffers took an interest in the project, wrote up a short blurb and posted it on the curated hackaday.com. I am very flattered by the attention and it was a great opportunity to see how other Hackaday users viewed the project.
The best comments are from people who appreciate the project and had constructive ideas and suggestions – this is what the site promised for project builders and I’m happy to see it working as intended.
There were a few variants of “This isn’t what I want. I want to see…” and while they are good project ideas, they’re not what I’m trying to accomplish here. Maybe they’ll feel inspired by my project to bring their own ideas to life!
And finally, the comments that dismissed the project. Pointing out shortcomings (some fair, some not) as criticisms without offering anything constructive to address the alleged issues. I just shrug off such criticism and focus on my work.
Positive or negative, the overall quality of the comments are far more articulate and intelligent than your average comment on YouTube.
I call that a win for Hackaday.





 After I got the Google sign-in working well enough for
After I got the Google sign-in working well enough for  The
The  Recently, web site security breaches have been a frequent topic of mainstream news. The technology is evolving but this chapter of technology has quite some ways to go yet. Learning web frameworks gives me an opportunity to understand the mechanics from web site developer’s perspective.
Recently, web site security breaches have been a frequent topic of mainstream news. The technology is evolving but this chapter of technology has quite some ways to go yet. Learning web frameworks gives me an opportunity to understand the mechanics from web site developer’s perspective.