The previous post described how I decided to position the PSU (Power Supply Unit). Once the position was decided, the next task is to determine the motherboard position.
The first challenge is my desire to accept a full-sized ATX motherboard. Full-sized boards are the easiest to work on and has the best feature set. They also have highest sales volume, which usually mean less expensive. I knew my project would be easier with a smaller microATX or Mini-ITX motherboard, but I wanted to accept full-size.
However, accepting the full size board doesn’t necessarily mean I intend to use all the expansion slots. In fact, I am happy to block the majority of them, leaving just the primary PCI-Express slot available to the GPU.
 The GPU itself is the next challenge. The primary slot is close to the CPU, which means it is going to stick up in the middle of the board, making the whole assembly awkward to fit. Again, I have an escape if I want it: there are PCIe extension ribbons available for purchase that allows more positioning flexibility for the GPU. They range from $89 well-regarded units from Digi-Key to $7 roll-of-the-dice units via mystery retailers on Amazon (*). I want to make this idea work without use of an extension, and avoid the variable that introduces to the system.
The GPU itself is the next challenge. The primary slot is close to the CPU, which means it is going to stick up in the middle of the board, making the whole assembly awkward to fit. Again, I have an escape if I want it: there are PCIe extension ribbons available for purchase that allows more positioning flexibility for the GPU. They range from $89 well-regarded units from Digi-Key to $7 roll-of-the-dice units via mystery retailers on Amazon (*). I want to make this idea work without use of an extension, and avoid the variable that introduces to the system.
While researching the layout, I learned the primary slot is not in the same position across all motherboards, adding to the challenge. While most boards position them in the slot closest to the CPU (all of the Mini-ITX boards have to by necessity) some of the boards place it in the second position. And since high-powered GPUs are two slots wide, that means I need to allow for three expansion slots worth of space.
 The GPU in the middle of the board leaves two rectangular volumes on either side: Both volume are candidates for use. One volume sits over the remaining expansion slots, and the other volume sits over the CPU.
The GPU in the middle of the board leaves two rectangular volumes on either side: Both volume are candidates for use. One volume sits over the remaining expansion slots, and the other volume sits over the CPU.
The volume over the expansion slots are predictable. ATX spec restricts height of motherboard components in order to maintain clearance for expansion cards. If I’m OK with the absence of cards, that entire volume can be reclaimed.
In contrast, the volume over the CPU is less predictable. While the ATX spec allocated volume to CPU and accessories (most significantly, the CPU cooler) that volume is highly variable. Stock CPU coolers typically take much less volume than allocated, and many fancy CPU coolers exceed the volume.
Given those two choices, it was an easy choice to snug the PSU up against the motherboard in the volume allocated to expansion cards that won’t be there.
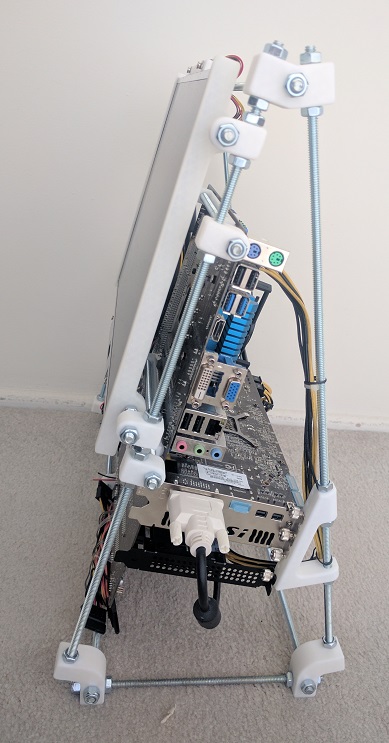
The last factor in positioning the motherboard is which direction I wanted the ports to be accessed. Pointing down is inconvenient to access. Pointing up makes ports vulnerable to damage from dropped items. So that leaves pointing left or right. Since the PSU power cable port is already on the right, I decided to face all the ports that way as well so everything the user needs to plug in is facing the same way.
All of the above considerations resulted in the PSU+motherboard layout I used.
Next post: Positioning the screen.
(*) Disclosure: As an Amazon Associate I earn from qualifying purchases.


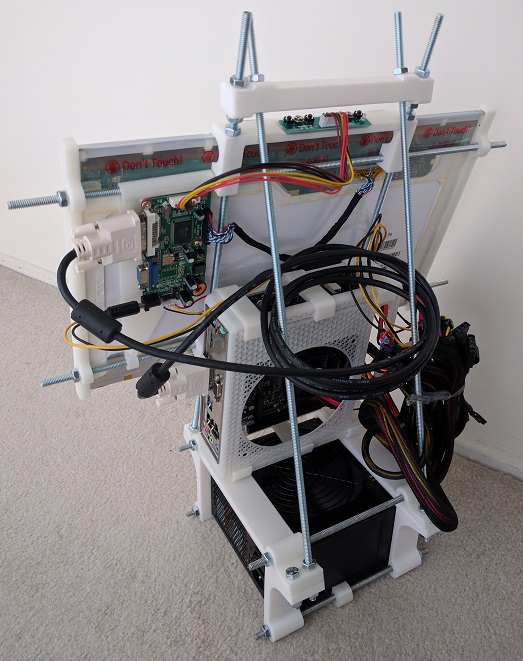
 The latest iteration of the home built luggable computer gets a fancy rotating screen to protect the screen while in transit and hold the screen up while in use.
The latest iteration of the home built luggable computer gets a fancy rotating screen to protect the screen while in transit and hold the screen up while in use. I’ve known about Hackaday for a while, both the professionally curated site
I’ve known about Hackaday for a while, both the professionally curated site 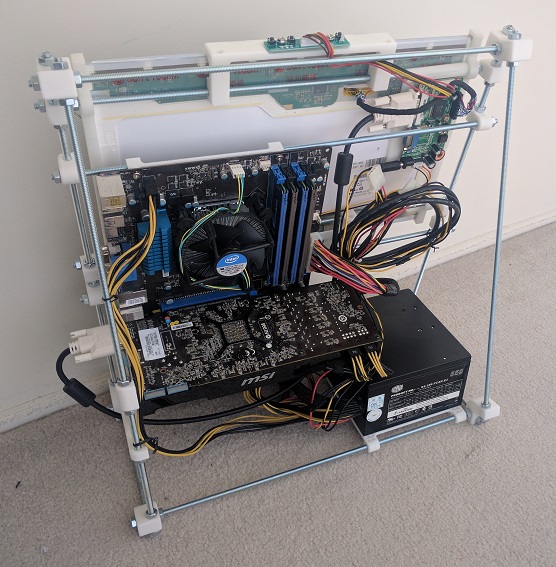





 After I got the Google sign-in working well enough for
After I got the Google sign-in working well enough for  Recently, web site security breaches have been a frequent topic of mainstream news. The technology is evolving but this chapter of technology has quite some ways to go yet. Learning web frameworks gives me an opportunity to understand the mechanics from web site developer’s perspective.
Recently, web site security breaches have been a frequent topic of mainstream news. The technology is evolving but this chapter of technology has quite some ways to go yet. Learning web frameworks gives me an opportunity to understand the mechanics from web site developer’s perspective.