 Amazon Web Services is a big, big ball of yarn. For somebody just getting started, the list of AWS products is quite intimidating. It’s not any fault of Amazon, it’s just the nature of building out such a comprehensive system. Fortunately, Amazon is not blind to the fact people can get overwhelmed and put admirable effort into a gentle introduction via their Getting Started resources: a series of (relatively) simple guided tours through select parts of the AWS domain.
Amazon Web Services is a big, big ball of yarn. For somebody just getting started, the list of AWS products is quite intimidating. It’s not any fault of Amazon, it’s just the nature of building out such a comprehensive system. Fortunately, Amazon is not blind to the fact people can get overwhelmed and put admirable effort into a gentle introduction via their Getting Started resources: a series of (relatively) simple guided tours through select parts of the AWS domain.
At the end of it all, though, a developer has to roll up their sleeves and dive in. The question then is: where? In previous times, I couldn’t make up my mind and got stuck. This time around, I have a starting point: Michael Hartl’s Ruby on Rails Tutorial sample app, which wants to store images on Amazon S3 (Simple Storage Service).
Let’s make it happen.
One option is to blaze the simplest, most direct path to get rolling, but I resisted. The example I found on stackoverflow.com granted the rails app full access to storage with my AWS root credentials. Functionally speaking that would work, but that is a very bad idea from a security practices standpoint.
So I took a detour through Amazon IAM (Identity and Access Management). I wanted to learn how to do a properly scoped security access scheme for the Rails sample app, rather than giving it the Golden Key to the entire kingdom. Unfortunately, since IAM is used to manage access to all AWS properties, it is a pretty big ball of yarn itself.
Eventually I found my on-ramp to AWS: A section in the S3 documentation that discussed access control via IAM. Since I control the rails app and my own AWS account, I was able to skip a lot of the cross-account management for this first learning pass, boiling it down to the basics of what I can do for myself to implement IAM best practices on S3 access for my Rails app.
After a few bumps in the exploration effort, here’s what I ended up with.
Root account: This has access to everything, so we want to use this account as little as possible to minimize risk of compromising this account. Login to this account just long enough to activate multi-factor authentication and create an IAM user account with “AdministratorAccess” privileges. Log out of the management console as root, log back in under the new admin account to do everything else.
Admin account: This account is still very powerful so it is still worth protecting. But if it should be compromised, it can at least be shut down without closing the whole Amazon account. (If root is compromised, all bets are off.) Use this account to set up the remaining items.
Storage bucket: While logged in as the admin account, go to the S3 service dashboard and create a new storage bucket.
Access policy: Go to the IAM dashboard and create a new S3 access policy. The “resource” of the policy is the storage bucket we just created. The “action” we allow are the minimum set needed for the rails sample app and no more.
- PutObject – this permission allows the rails app to upload the image file itself.
- PutObjectAcl – this permission allows the rails app to change the access permission on the image object, make the image publicly visible to the world. This is required for use as the source field of an HTML <img> tag in the rails app.
- DeleteObject – when a micropost is deleted, the app needs this permission so the corresponding image can be deleted as well.
Access group: From the IAM dashboard, create a new access group. Under the “Permissions” list of the group, attach the access policy we just created. Now any account which is a member of the group has enough access the storage bucket to run the rails sample app.
User: From the IAM dashboard, create a new user account to be used by the rails app. Add this newly user to the access group we just created, so it is a part of the group and can use the access policy we created. (And no more.)
This new user, which we granted only a low level of access, will not need a password since we’ll never log in to Amazon management console with it. But we will need to generate an app access key and secret key.
Once all of the above are done, we have everything we need to put into Heroku for the Rails Tutorial sample app. A S3 storage bucket name, plus the access and secret key of the low level user account we created to access that S3 storage bucket.
While this is far more complex than the stackoverflow.com answer, it is more secure. Plus a good exercise to learn the major bits and pieces of an AWS access control system.
The above steps will ensure that, if the Rails sample app should be compromised in any way, the hacker has only the permissions we granted to the app and no more. While the hacker can put new images on the S3 bucket and make them visible, or delete existing images, but they can’t do anything else in that S3 bucket.
And most importantly, the hacker has no access to any other part of my AWS account.
 The Ruby on Rails Tutorial was a great way for developers like me to get up and running with no prior Rails experience. However, it does require the reader to have some level of computer software skill so complete beginners could still get lost.
The Ruby on Rails Tutorial was a great way for developers like me to get up and running with no prior Rails experience. However, it does require the reader to have some level of computer software skill so complete beginners could still get lost. Recently, web site security breaches have been a frequent topic of mainstream news. The technology is evolving but this chapter of technology has quite some ways to go yet. Learning web frameworks gives me an opportunity to understand the mechanics from web site developer’s perspective.
Recently, web site security breaches have been a frequent topic of mainstream news. The technology is evolving but this chapter of technology has quite some ways to go yet. Learning web frameworks gives me an opportunity to understand the mechanics from web site developer’s perspective.
 My new concept of the day:
My new concept of the day:  Amazon Web Services is a big, big ball of yarn. For somebody just getting started, the
Amazon Web Services is a big, big ball of yarn. For somebody just getting started, the
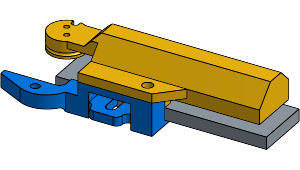
 And now another entry in the “3D printer is not the solution to everything” file.
And now another entry in the “3D printer is not the solution to everything” file.
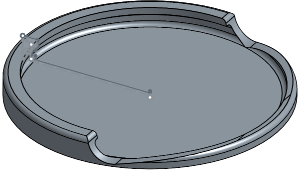
 Up until this point I used Cura 2.x, which met all of my STL to G-code slicing needs. But the caliper battery tray project demanded more.
Up until this point I used Cura 2.x, which met all of my STL to G-code slicing needs. But the caliper battery tray project demanded more.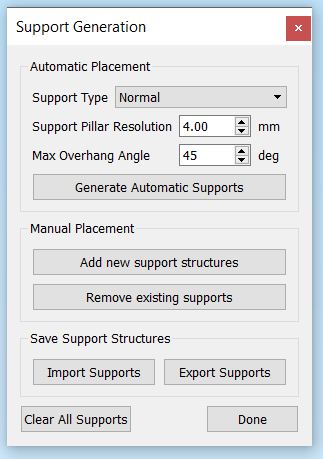
 I had been using
I had been using 
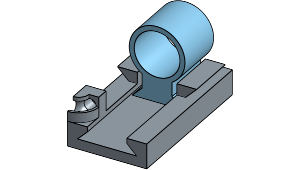 And now, a story of failure not the fault of the 3D printer. The previous project allowed my Nexus 5X phone to sit correctly in the Utopia 360 VR viewer. This project addresses the next problem: the need to tap the screen during use of the VR app.
And now, a story of failure not the fault of the 3D printer. The previous project allowed my Nexus 5X phone to sit correctly in the Utopia 360 VR viewer. This project addresses the next problem: the need to tap the screen during use of the VR app.

 Earlier this week Google officially released details about their upcoming
Earlier this week Google officially released details about their upcoming 
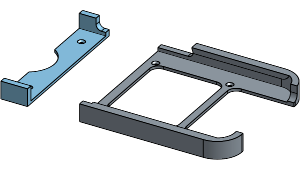
 I’ve enjoyed using my 3D printer to solve little problems around the house. This project was extra amusing: I wanted to solve a problem I had with my 3D printer that I wanted to solve with the 3D printer.
I’ve enjoyed using my 3D printer to solve little problems around the house. This project was extra amusing: I wanted to solve a problem I had with my 3D printer that I wanted to solve with the 3D printer.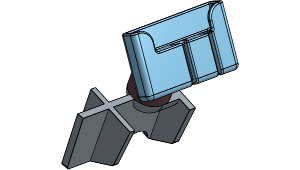 Given how popular it is to have mapping and navigation on the phone, there are a lot of phone mount products on the market. Unfortunately, given the diversity of phones and of cars, it isn’t feasible for product manufacturers to custom make individual design for every car + phone combination, so every mount is a generalized trade-off of some sort.
Given how popular it is to have mapping and navigation on the phone, there are a lot of phone mount products on the market. Unfortunately, given the diversity of phones and of cars, it isn’t feasible for product manufacturers to custom make individual design for every car + phone combination, so every mount is a generalized trade-off of some sort.
 Spotting scopes sold for bird watchers and rifle marksmen can be quite inexpensive compared to serious camera lenses of similar zoom capability. I knew there was a difference in the picture quality but wanted to try it first hand.
Spotting scopes sold for bird watchers and rifle marksmen can be quite inexpensive compared to serious camera lenses of similar zoom capability. I knew there was a difference in the picture quality but wanted to try it first hand.

 Nowadays people are familiar with recycling. But some people forget recycling is only the third alternative in “reduce, reuse, recycle.” The goal of this project is to reuse small glass jars instead of tossing them into glass recycle.
Nowadays people are familiar with recycling. But some people forget recycling is only the third alternative in “reduce, reuse, recycle.” The goal of this project is to reuse small glass jars instead of tossing them into glass recycle.